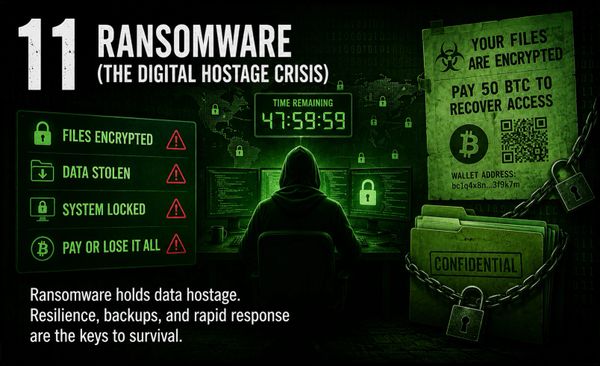
“The Ten Fatal Flaws” introduces the core idea behind Digital Fortress Opera – Volume 1: many of the most damaging cybersecurity failures are not mysterious or exotic. They are recurring weaknesses that appear when systems are built too quickly, configured carelessly, monitored poorly, or trusted too easily. The song moves through ten common flaws that continue to affect modern organizations, from insecure code and weak authentication to exposed data, poor visibility, access control failures, and human-targeted attacks. Each flaw represents a crack in the digital fortress, but each can also be addressed through secure design, disciplined operations, strong governance, and a culture that treats cybersecurity as a shared responsibility.
Video Link Below:
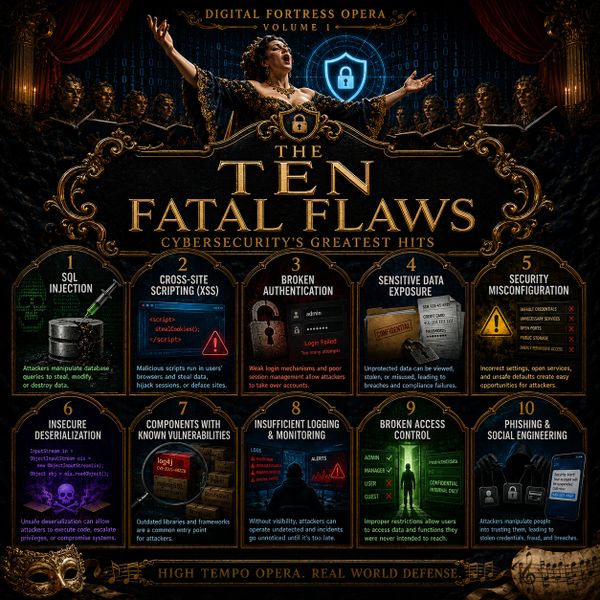
SQL Injection
SQL injection occurs when an application accepts user input and passes it into a database query without proper validation or protection. An attacker may be able to manipulate the query, retrieve unauthorized data, modify records, or damage the database. This flaw has existed for decades, yet it remains dangerous because many systems still rely on poorly handled input and overly trusted application logic. Defending against SQL injection requires parameterized queries, input validation, least-privilege database access, secure coding standards, and regular testing.

Cross-Site Scripting
Cross-site scripting, often called XSS, allows attackers to inject malicious scripts into web pages viewed by other users. Instead of attacking the server directly, XSS abuses the trust between a user and a website. A successful attack can steal session cookies, capture user activity, redirect victims, or perform actions on behalf of the user. Preventing XSS requires careful output encoding, input validation, secure content handling, browser protections, and frameworks that reduce unsafe script execution.

Broken Authentication
Broken authentication happens when systems fail to properly verify identity or protect user sessions. Weak passwords, poor session management, missing multi-factor authentication, credential reuse, and insecure password recovery processes can all allow attackers to impersonate legitimate users. Because identity is the front door to most digital systems, authentication failures can quickly become full account compromise. Strong authentication requires multi-factor authentication, secure session handling, password protections, monitoring for suspicious login behavior, and clear identity governance.
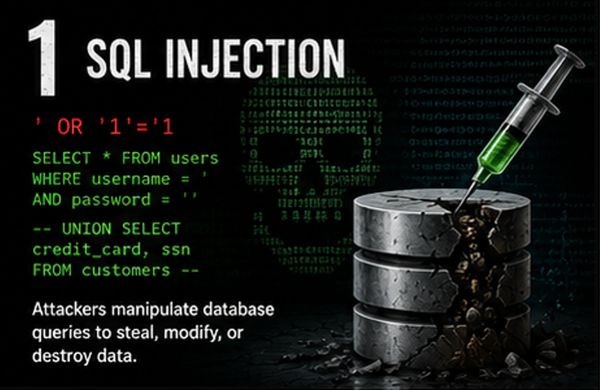
Sensitive Data Exposure
Sensitive data exposure occurs when important information is stored, transmitted, or displayed without adequate protection. This may include passwords, personal information, financial records, intellectual property, operational data, or credentials. Exposure can happen through weak encryption, poor access controls, logging sensitive information, misconfigured storage, or transmitting data in plain text. Protecting sensitive data requires encryption, data classification, access control, key management, secure storage, careful logging practices, and a clear understanding of where critical data lives.

Security Misconfiguration
Security misconfiguration is one of the most common and preventable cybersecurity problems. It happens when systems, applications, cloud services, network devices, or identity platforms are left with unsafe settings, default credentials, unnecessary services, exposed interfaces, or overly permissive access. Misconfiguration often creates easy opportunities for attackers because the weakness is already present before exploitation begins. Reducing this risk requires secure baselines, configuration management, automated checks, patching discipline, hardening guides, and regular review of exposed services and permissions.

Insecure Deserialization
Insecure deserialization occurs when an application accepts serialized data and reconstructs it into an object without properly verifying that the data is safe. Attackers may manipulate that data to change application logic, escalate privileges, execute code, or trigger unexpected behavior. This flaw can be difficult to understand because it often hides inside application workflows and software design patterns. Defenses include avoiding unsafe deserialization when possible, validating and signing serialized data, limiting object types, applying least privilege, and testing application logic for abuse cases.

Using Components with Known Vulnerabilities
Modern software depends on libraries, frameworks, packages, containers, operating systems, and third-party components. When those components contain known vulnerabilities and remain unpatched, attackers can use publicly available exploit information to compromise systems. This risk is especially serious because organizations may not always know what components they are running or where vulnerable dependencies exist. Reducing this risk requires asset inventory, software composition analysis, vulnerability management, timely patching, dependency review, and lifecycle planning for unsupported software.

Insufficient Logging and Monitoring
Insufficient logging and monitoring means an organization cannot reliably see what is happening inside its environment. Without useful logs, alerting, and review processes, attackers may move through systems undetected, maintain persistence, or exfiltrate data before anyone notices. Visibility is a core security capability because prevention will never be perfect. Strong logging and monitoring require collecting meaningful events, protecting logs from tampering, correlating activity across systems, alerting on suspicious behavior, and ensuring people and processes exist to respond.

Broken Access Control
Broken access control occurs when users can reach data, systems, or functions they should not be allowed to access. This may include viewing another user’s records, performing administrative actions without permission, bypassing authorization checks, or abusing overly broad roles. Access control failures are dangerous because authenticated users may still become unauthorized actors once inside the system. Defending against this flaw requires least privilege, role-based or attribute-based access control, server-side authorization checks, regular permission reviews, and testing for privilege escalation.

Phishing and Social Engineering
Phishing and social engineering target people rather than software flaws. Attackers use urgency, fear, curiosity, authority, or trust to trick users into clicking links, opening attachments, sharing credentials, approving requests, or bypassing normal procedures. These attacks remain effective because humans are part of every security system. Reducing phishing risk requires user education, phishing-resistant multi-factor authentication, email security controls, reporting processes, verification habits, and a culture where employees are encouraged to pause, question, and report suspicious activity.
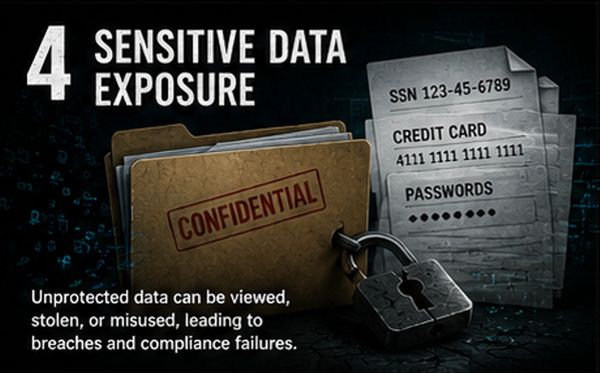
Ransomware and Digital Extortion
Ransomware and digital extortion occur when attackers compromise systems, steal or encrypt data, and pressure victims into paying to restore operations or prevent public exposure. These attacks often spread through phishing, stolen credentials, exposed remote access, unpatched systems, or vulnerable third-party tools. Once inside, attackers may move laterally, disable backups, disrupt services, and turn an organization’s own data into leverage.
Reducing ransomware risk requires resilient backups, phishing-resistant multi-factor authentication, least privilege, network segmentation, rapid patching, endpoint protection, tested recovery plans, and monitoring that can detect suspicious activity before a compromise becomes a crisis.
This website uses cookies.
We use cookies to analyze website traffic and optimize your website experience. By accepting our use of cookies, your data will be aggregated with all other user data.